Canonical has confirmed that its Ubuntu web infrastructure is under a sustained cross-border DDoS attack, resulting in outages across public-facing Ubuntu services.
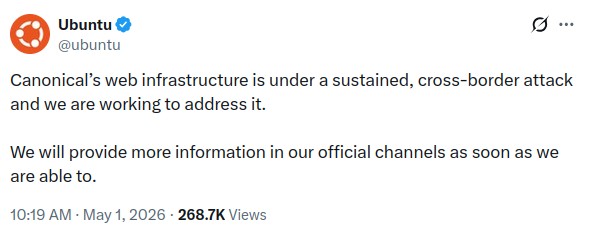
The company acknowledged the incident in an official Ubuntu Discourse announcement, stating that Canonical’s web infrastructure is under attack and that it is working to resolve the issue. The notice did not include technical details, identify the attackers, or specify when full service would be restored.
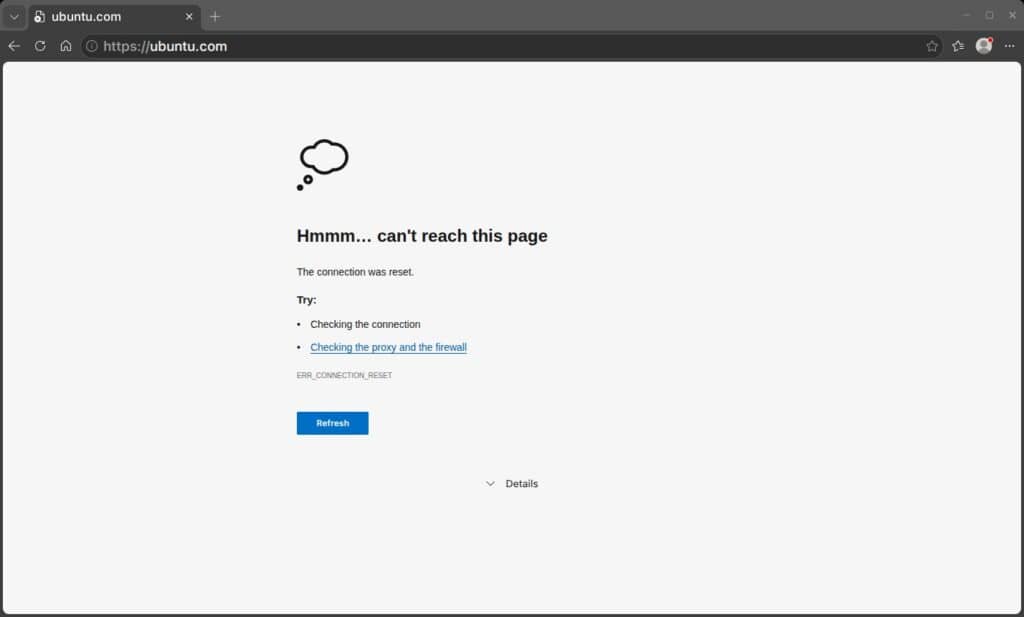
The outage has disrupted access to Ubuntu-related web services, with users reporting connection failures and interruptions on ubuntu.com and related infrastructure. Canonical’s status page lists active incidents affecting both Canonical and Ubuntu services.
Importantly, a distributed denial-of-service attack does not indicate a system breach. In these incidents, attackers typically overwhelm a service with traffic, causing it to slow, become unstable, or become unreachable.
This disruption follows a similar incident affecting Arch Linux in August 2025, when the project confirmed a DDoS attack on its main website, the Arch User Repository, and project forums. At that time, Arch reported that the attack mainly impacted public-facing services, not the distribution’s package integrity.
Now with this, the Ubuntu incident becomes part of a broader trend in which Linux distribution infrastructure has become a visible target for availability attacks. At the time of writing, Canonical has not publicly said what motivated the attack.
While some reports mention claims of responsibility by a hacktivist group, Canonical has not attributed the incident to any party. Until further details are provided, the confirmed facts remain limited to a sustained DDoS attack affecting Canonical and Ubuntu web infrastructure.

” there are also lots of infected android tv boxes being sold from Chinese companies. It is better to use western brands.”
Like your computer or phone made in china? for the sake of argument you’ll probably say “NOPE, MINE’S NOT!” but they probably are. How do we audit hardware made in china?
About the best you can do is buy devices that let you install your own os like linux for pc or grapheneos for android which is open source. There are other things beyond the os that would be extremely hard if not impossible to change unless a open source option exist already. I have a older android phone with grapheneos that did not work with some of my work apps so I ended up buying another phone without grapheneos that was not made in china but my pixel was made in china which I will retire once grapheneos no longer supports it. You still need to be careful on android since open source does not always mean something is safe and sticking to trustworthy software sources and the same with linux regarding how or where you get your software and restraint can be a good security measure.
not really sure since I could never audit. probably have to pay a company that has the know how to do it.
Hopefully the figure it out soon. To bad they do not use something like cloudflare ddos protection that could help stop or even prevent such attacks.
I guess these linux distros do not want to use cloudflare protection since its not open source? I would still use a distro if they used it only to stop things like this since it is very hard to stop compared to huge corporations with more resources.
I saw a report just a few hours ago that said it was Iranians, or possibly hackers who are rooting for Iran in the current situation.
I guess ubuntu is a easier target then say amazon or micosoft who are much larger and probably have better protection from ddos attacks.
Accoridng to cloudflare attacks have gone way up in recent years and there is a ton of infected android tvs that are part of a botnet. https://blog.cloudflare.com/ddos-threat-report-2025-q4/
lots of people installed SmartTube that could have been infected for years. The guy that maintains the project was supposedly hacked he did not know about it till google flagged the app supposedly and people started complaining. Nobody really knows who he is and there are also lots of infected android tv boxes being sold from Chinese companies. It is better to use western brands. Then you have websites and people on youtube pushing people to install piracy apps that could be letting hackers gain access.
i have seen web articles and youtube videos on acemagic pc’s from china being preinstalled with windows os that has malware preinstalled and even after they said they fixed the issue newer pcs still had malware.