Pangolin, an open-source, self-hosted identity-based remote access platform that combines a tunneled reverse proxy with zero-trust VPN-style access, has released v1.17.
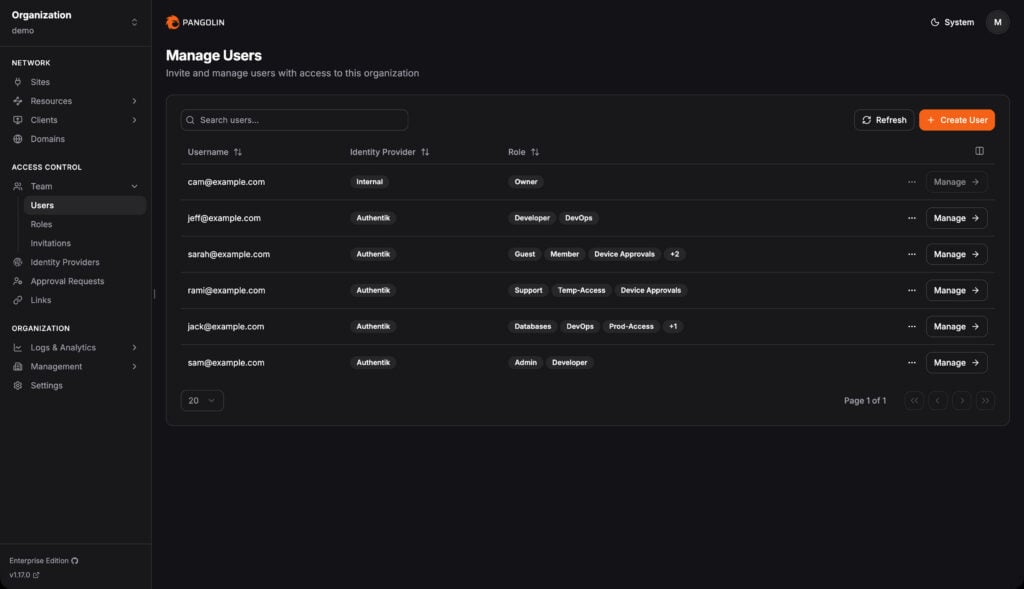
The most striking feature is the added support for multiple roles per user. Previously, users could have only one role, limiting the flexibility of access control. Now, users can be assigned multiple roles, enabling administrators to grant access based on the combined permissions of all assigned roles.
This update also enhances identity provider role mapping. For auto-provisioned users, administrators can now assign roles using fixed roles, a new mapping builder that translates identity provider role or group IDs into Pangolin roles without coding, or raw JMESPath expressions for advanced configurations.
Moreover, Pangolin 1.17 adds built-in Google and Azure templates for global identity providers at the server-wide level. Regarding site provisioning keys, administrators can now, instead of generating and distributing individual IDs and secrets for each deployment, use a long-lived token that allows sites to obtain credentials automatically at startup.
Pangolin 1.17 is now capabale to records raw TCP and UDP sessions between clients and private resources, providing an audit trail of user access, timing, and session duration. This feature applies to zero-trust private resources on the Pangolin network, as public browser-based resources already include access logging.
Finally, the release introduces log streaming, enabling Pangolin to forward events to third-party data collectors, including Datadog, Splunk, and Microsoft Sentinel. Administrators can specify destinations, select push methods like HTTP or S3, and choose which log types to export.
For more details, see the announcement or refer to the changelog.
Image credits: Panglolin