Rocky Linux has launched an optional Security Repository to provide urgent fixes in exceptional security cases before upstream Enterprise Linux packages are released.
The repository is intended for cases where a significant vulnerability is public, exploit code exists, and waiting for upstream packages would leave systems exposed. It is disabled by default, so standard update behavior remains unchanged unless accelerated security fixes are needed.
This approach is a limited exception to Rocky Linux’s upstream-compatible model. In other words, the repository is not intended as a general fast-track update channel or a replacement for the standard release process.
Additionally, keep in mind that the packages from the Security Repository are versioned for automatic replacement by later upstream Enterprise Linux updates; they do not include traditional errata records and do not appear through dnf update --security as standard advisories.
The first use case involved Dirty Frag, a set of Linux kernel local privilege escalation vulnerabilities. Dirty Frag included two CVEs: one affecting ESP and another affecting RxRPC through the kernel-modules-partner package. The initial Security Repository kernel included fixes for both.
Red Hat has since addressed the ESP vulnerability in its latest builds. Rocky’s second kernel release included this upstream fix and continued to address the RxRPC issue. However, Rocky is now dropping the RxRPC patch because Red Hat does not ship the affected kernel-modules-partner package to customers, and Rocky only includes it in its development repository without support guarantees.
Rocky Linux states the Security Repository functioned as intended by bridging the gap until an upstream fix was available, without maintaining an independent patch for a package not intended for production systems.
If Rocky provides a temporary fix and upstream does not address the issue, the next upstream kernel release may supersede Rocky’s patched package. Users who have not version-locked the kernel could lose the temporary fix. Rocky notes this is a trade-off of remaining an Enterprise Linux rebuild rather than maintaining an independent kernel fork.
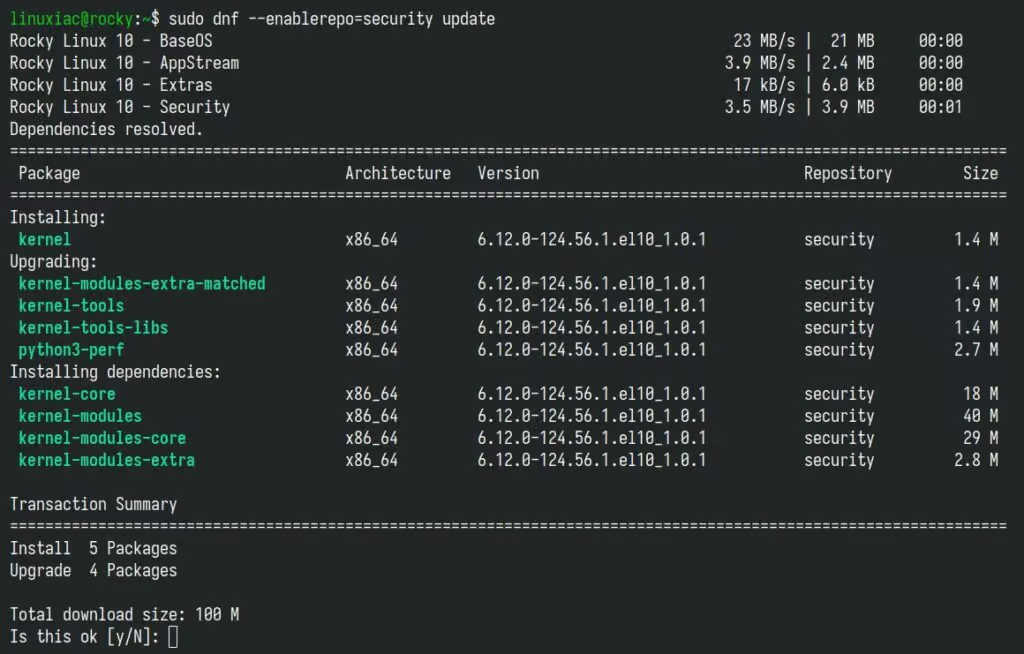
Administrators who want to apply available fixes from the Security Repository can run:
sudo dnf --enablerepo=security updateCode language: Bash (bash)To enable the repository permanently, use the standard DNF repository configuration. No action is required for systems that do not need accelerated fixes; their update behavior will remain unchanged.
Rocky Linux will notify users when packages are added to the repository, what they address, and the expected transition back to upstream-aligned packages.
For more details, see the announcement or check out Rocky’s blog post on the subject.
